Endpoint Detection and Response (EDR) has emerged as a cornerstone of modern cybersecurity, empowering defenders to identify and quarantine malicious activities on endpoints before attackers can escalate. At its best, EDR solutions combine real-time behavioral analytics, advanced threat intelligence, and incident response features to safeguard laptops, servers, and other critical devices. Yet as the cybersecurity landscape continues to evolve, attackers have become adept at circumventing these defenses through stealthier techniques. This escalating arms race underscores why EDR bypass testing is no longer a mere optional exercise—it is a strategic necessity for organizations that take security seriously.
EDR solutions gained popularity in the past decade as a more proactive alternative to traditional antivirus software. Rather than relying solely on static signatures, EDR platforms scan for unusual behaviors such as processes hijacking system calls, unexpected privilege escalations, or stealthy lateral movements across the network. They often record historical logs of system events, enabling security teams to piece together intrusions that might otherwise go unnoticed. By consolidating alerts and forensic data, EDR aims to cut dwell times from weeks or months to mere hours. Given that many major breaches begin at the endpoint—through phishing emails, rogue USB drives, or drive-by downloads—Evolving EDR solutions help defenders maintain a critical line of defense.
Despite this substantial progress, sophisticated adversaries have responded in kind. Attackers today craft malicious code that evades sandbox detection, randomizes known indicators of compromise (IOCs), and disables or misleads EDR processes. Some leverage kernel exploits to slip beneath user space monitoring, while others cloak payloads within legitimate software processes to avoid triggering suspicious behaviors. Ransomware groups have even published step-by-step guides on how to kill specific EDR processes or hide malicious files from real-time scanning. These adversarial tactics highlight why an EDR deployment that goes unchallenged can lull defenders into a false sense of security. Without actively testing how an EDR solution handles advanced intrusion attempts, organizations have no reliable measure of whether their chosen platform’s real-world protection aligns with marketing promises.
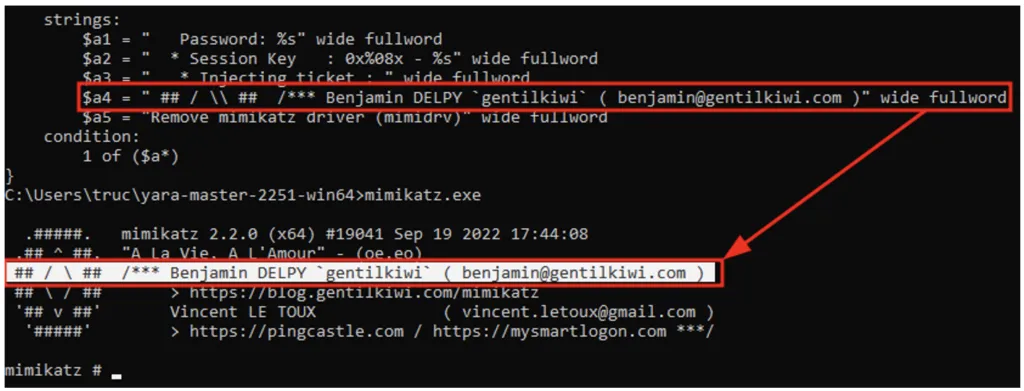
EDR bypass testing, also known as adversarial testing or EDR evasion testing, involves simulating attacker techniques specifically designed to slip past endpoint defenses. Security professionals or red teams create benign but suspicious executables, manipulate memory injections, and replicate known adversarial playbooks—everything from scripting out Powershell bypass commands to unleashing custom-coded droppers. The aim is to replicate the strategies criminals might use to avoid detection. Although this testing process requires specialized skills, it offers a powerful reality check. If a bypass attempt succeeds, security teams glean valuable insight: they can discover which detection rules need tuning, which behaviors slip under the radar, and whether the EDR solution’s advanced machine learning (ML) or behavioral analytics hold up under real, creative adversarial pressure.
A common misconception is that performing a single EDR bypass test offers a definitive grade—“pass” or “fail.” In truth, the process is iterative. Attackers continually refine methods, and product vendors roll out patches or updated detection logic in response. On top of that, each organization’s environment has unique configurations, group policies, and user behaviors that can influence detection thresholds. A bypass that works in a test lab might fail if the real production environment has a certain security control or if the EDR agent is configured more restrictively. Conversely, a technique that evades detection in one environment could fail in another that employs different scanning heuristics or custom detection rules. For these reasons, robust EDR bypass testing extends over time, tracking improvements and verifying that new EDR updates don’t introduce unexpected blind spots.
From a risk management standpoint, EDR bypass testing delivers crucial insights on where to invest in additional layers of defense. For instance, consider a scenario where red teamers discover that executing malicious code in memory, without touching the disk, bypasses the EDR’s file scanning mechanisms. While the vendor might fix that gap in a future release, the organization could also address it by implementing additional memory forensics, restricting script interpreters, or strengthening user behavior analytics. The test outcome becomes a catalyst for a layered security approach—integrating Identity and Access Management (IAM), network segmentation, and SIEM correlation to reduce reliance on a single protective technology. When defenders see the kill chain in action, they can identify which triggers or anomalies should be flagged earlier to short-circuit the intrusion.
Organizations also benefit from verifying whether their incident response workflows align with real bypass scenarios. Even if an EDR solution logs suspicious activity but fails to generate a high-priority alert, defenders might miss the intrusion for hours or days. By intentionally bypassing EDR detection, red teams can gauge how quickly a malicious pattern is flagged by SOC analysts—if at all—and how effectively they escalate it. If defenders remain unaware of the infiltration until after final exfiltration or mock sabotage, that indicates a gap in visibility or alert triage. EDR bypass testing shines light not just on the technical blind spots but also on process or staffing issues in the SOC. Achieving full coverage means ensuring that even partial EDR alerts, combined with other sensors (like network monitoring or threat intelligence feeds), steer investigators to the intruder’s presence.
Another advantage of systematic EDR bypass testing is fostering healthy vendor relationships. Some vendors incorporate or even encourage adversarial test results from clients to refine their detection algorithms. For example, if a red team repeatedly bypasses EDR through a novel process hollowing technique or by tinkering with known Windows binaries, reporting that method helps the vendor’s development team to patch that gap for all customers. Meanwhile, as an organization invests in advanced, multi-year licensing, it can evaluate how quickly the vendor responds to newly discovered evasion tactics. The speed of these fixes and updates speaks volumes about the vendor’s commitment to staying ahead of emerging threats. In an environment where criminals churn out new variants of malware daily, a slow or unresponsive vendor can degrade an organization’s overall security posture.
Integrating EDR bypass testing also fosters a culture of continuous improvement. Security staff grow more adept at discovering the subtle artifacts that remain even after a bypass. Attackers might clear event logs, but forensic investigators can spot residual memory anomalies or missing data in other logs. If defenders train themselves to detect these second-order signals, they become more resilient to future evasion attempts. Over time, those learnings feed back into the EDR solution’s custom detection rules or refined policies. For instance, if repeated successful bypass attacks rely on disabling Windows Event Logging, the organization could adopt a policy that triggers an immediate alarm when that logging is tampered with—an alarm that can overshadow some bypass attempts entirely.
However, implementing EDR bypass testing is not straightforward. It often requires specialized knowledge and careful scoping. Red teams and security consultancies typically abide by rules of engagement that define what actions are allowed and which systems remain off-limits. Some organizations worry about disruptions if testers inadvertently trigger real destructive behaviors. Realistic simulations can come close to actual sabotage if the testers aren’t governed by explicit boundaries. Another concern is that the EDR vendor might interpret these tests as malicious, inadvertently blacklisting test infrastructure or interfering with normal operations. Clear communication—ensuring the vendor knows to expect controlled tests—can alleviate this friction. Some advanced EDR products even offer “testing modes,” letting red teams assess detection logic without causing undue alarms or quarantining benign test scripts.
Another potential obstacle is the cost of running repeated bypass tests. Skilled red teams, especially those proficient in advanced adversarial tactics, command high fees. Smaller businesses might balk at the expense, feeling that a single solution from a reputable EDR vendor should suffice. Yet the cost of ignoring hidden gaps can far outweigh the expense of a professional assessment—particularly if an actual breach leads to downtime, ransom payments, legal liabilities, and reputational harm. Even modest simulations or internal purple team exercises, where in-house defenders and testers collaborate closely, can yield significant returns. These lower-scale efforts might not replicate every advanced technique, but they still uncover common misconfigurations or partial detection failures.
Regulatory developments and cyber insurance trends also place a spotlight on EDR bypass testing. In certain industries, regulators demand proof of robust threat detection and incident response capabilities. By demonstrating ongoing adversarial assessments, an organization can show it’s not just relying on vendor claims but verifying real-world efficacy. Cyber insurers, too, may require clients to periodically validate their endpoint security, factoring test results into policy premiums or coverage limits. If an insurer sees repeated successful bypass attempts without swift remediation, they might adjust the risk rating accordingly. Thus, organizations that integrate bypass testing into their broader compliance and risk management strategy stand to gain financial and reputational advantages over peers that remain complacent.
Moving forward, EDR bypass tactics will continue to evolve. Attackers frequently abuse legitimate tools like PowerShell, WMI, or living-off-the-land binaries to blend in. They may inject malicious payloads into trusted processes or utilize advanced stealth frameworks that generate ephemeral code in memory. By the time a security product logs unusual calls, the attacker has already pivoted to another method. Hence, bypass testing must keep pace with these dynamic trends. A single “snapshot” test or an annual assessment might leave organizations with stale results, failing to reflect new exploits or novel evasion frameworks. Continuous or quarterly test cycles can detect emergent patterns and ensure the EDR solution remains tuned to detect them.
In parallel, defenders should consider how other solutions integrate with or complement their EDR. A well-honed SIEM (Security Information and Event Management) or XDR (Extended Detection and Response) platform can correlate suspicious endpoint events with network logs or cloud telemetry, potentially identifying threats that slip past endpoint scanning alone. Identity and access management systems can require multi-factor authentication for administrative tasks, mitigating the damage an attacker can do even if they bypass EDR initially. Meanwhile, threat intelligence feeds can alert defenders to new adversarial techniques that have succeeded against certain EDR products, prompting the internal team to test and fix those particular gaps. This synergy ensures that the endpoint protection does not exist in isolation but forms part of a cohesive, layered security strategy.
Ultimately, EDR bypass testing exemplifies the proactive mindset needed in cybersecurity. Organizations cannot rely on marketing claims or single-time third-party reviews to guarantee that their endpoint solution is airtight. Regular, realistic adversarial testing—carried out by skilled professionals and integrated into incident response drills—reveals the difference between theoretical security and operational resilience. This iterative process sharpens detection rules, streamlines forensic workflows, and shapes a culture of adaptability in the face of evolving threats. When done correctly, bypass testing elevates an EDR solution from a black box into a transparent, rigorously vetted system—one that stands ready for the relentless creativity of modern attackers.